Disclaimer: This blog post was written when Quantum Xchange was focused on building and selling the first quantum network in the U.S.
We have since pivoted our business and product offering, with the invention of Phio Trusted Xchange (TX), a first-of-its-kind quantum-safe, out-of-band key delivery system. While our technology offering can support QKD deployments, we are not a quantum communications provider or reseller. Our quantum-safe key exchange supports quantum keys generated from any source(QRNG or QKD) protected by any method (all PQC key encapsulation algorithms).
Quantum cryptography sounds fairly complex – probably because it is. That’s why we put together this “encryption guide for dummies” as a way of explaining what quantum cryptography is and taking some of the complexity out of it.
Although the subject has been around for a couple of decades, quantum cryptography (not to be confused with post-quantum cryptography) is quickly becoming more critically relevant to our everyday lives because of how it can safeguard vital data in a way that current encryption methods can’t.
Consider, for example, the trust you place in banks and commercial enterprises to keep your credit card and other information safe while conducting business transactions online. What if those companies – using current encryption methods – could no longer guarantee the security of your private information? Granted, cybercriminals are always trying to gain access to secure data, but when quantum computers come online, that information will be even more vulnerable to being hacked. In fact, hackers don’t even need to wait for quantum computers to start the process because they’re collecting encrypted data now to decrypt later when the quantum computers are ready. With quantum encryption, that’s not the case because your information will be unhackable. Let’s explain.
What is Quantum Cryptography?
Cryptography is the process of encrypting data, or converting plain text into scrambled text so that only someone who has the right “key” can read it. Quantum cryptography, by extension, simply uses the principles of quantum mechanics to encrypt data and transmit it in a way that cannot be hacked.
While the definition sounds simple, the complexity lies in the principles of quantum mechanics behind quantum cryptography, such as:
- The particles that make up the universe are inherently uncertain and can simultaneously exist in more than one place or more than one state of being.
- Photons are generated randomly in one of two quantum states.
- You can’t measure a quantum property without changing or disturbing it.
- You can clone some quantum properties of a particle, but not the whole particle.
All these principles play a role in how quantum cryptography works.
What’s the difference between post-quantum cryptography and quantum cryptography?
Post-quantum cryptography refers to cryptographic algorithms (usually public-key algorithms) that are thought to be secure against an attack by a quantum computer. These complex mathematical equations take traditional computers months or even years to break. However, quantum computers running Shor’s algorithm will be able to break math-based systems in moments.
Quantum cryptography, on the other hand, uses the principles of quantum mechanics to send secure messages, and unlike mathematical encryption, is truly un-hackable.
Unlike mathematical encryption, quantum cryptography uses the principles of quantum mechanics to encrypt data and making it virtually unhackable.
@Quantum_Xchange
How Quantum Cryptography Works
Quantum cryptography, or quantum key distribution (QKD), uses a series of photons (light particles) to transmit data from one location to another over a fiber optic cable. By comparing measurements of the properties of a fraction of these photons, the two endpoints can determine what the key is and if it is safe to use.
Breaking the process down further helps to explain it better.
- The sender transmits photons through a filter (or polarizer) which randomly gives them one of four possible polarizations and bit designations: Vertical (One bit), Horizontal (Zero bit), 45 degree right (One bit), or 45 degree left (Zero bit).
- The photons travel to a receiver, which uses two beam splitters (horizontal/vertical and diagonal) to “read” the polarization of each photon. The receiver does not know which beam splitter to use for each photon and has to guess which one to use.
- Once the stream of photons has been sent, the receiver tells the sender which beam splitter was used for each of the photons in the sequence they were sent, and the sender compares that information with the sequence of polarizers used to send the key. The photons that were read using the wrong beam splitter are discarded, and the resulting sequence of bits becomes the key.
If the photon is read or copied in any way by an eavesdropper, the photon’s state will change. The change will be detected by the endpoints. In other words, this means you cannot read the photon and forward it on or make a copy of it without being detected.
An example of how quantum encryption works:
Imagine you have two people, Alice and Bob, who want to send a secret to each other that no one else can intercept. With QKD, Alice sends Bob a series of polarized photons over a fiber optic cable. This cable doesn’t need to be secured because the photons have a randomized quantum state.
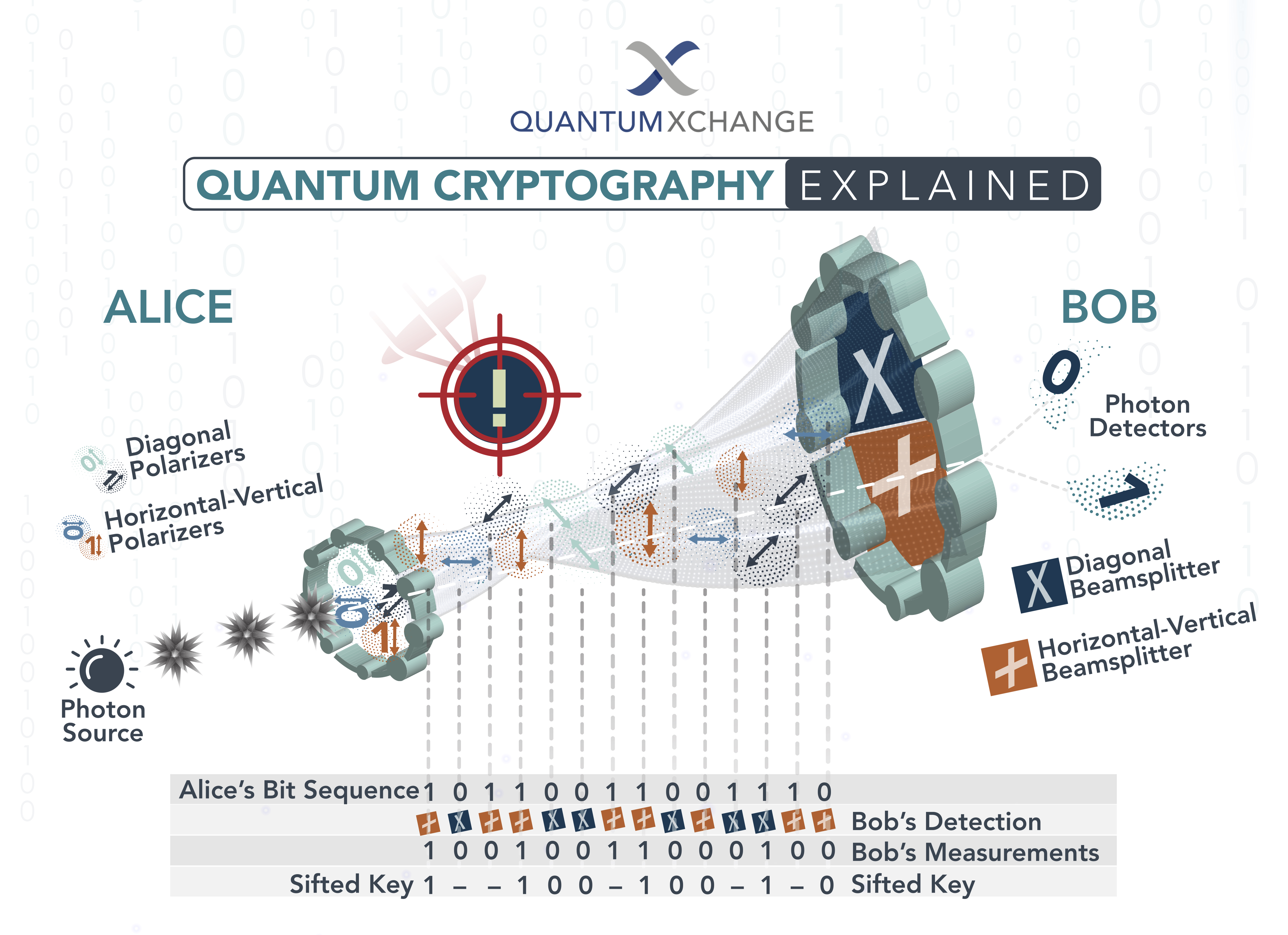
If an eavesdropper, named Eve, tries to listen in on the conversation, she has to read each photon to read the secret. Then she must pass that photon on to Bob. By reading the photon, Eve alters the photon’s quantum state, which introduces errors into the quantum key. This alerts Alice and Bob that someone is listening and the key has been compromised, so they discard the key. Alice has to send Bob a new key that isn’t compromised, and then Bob can use that key to read the secret.
The Solution We Need Now for Tomorrow
The need for unbreakable encryption is staring us in the face. With the development of quantum computers looming on the horizon, the integrity of encrypted data is at risk now. Fortunately, quantum cryptography, through QKD, offers the solution we need to safeguard our information well into the future – all based on the complex principles of quantum mechanics.
As the need for unbreakable encryption looms in networks around the world, quantum cryptography is the solution that will safeguard and future-proof sensitive information.
@Quantum_Xchange
For more information on Quantum Xchangehange and how we can provide future-proof, unbreakable encryption, contact us at quantumxc.com