Defending Encryption: Quantum XChange at Cisco Live Amsterdam

Defending Encryption: Quantum XChange at Cisco Live Amsterdam
Securing the Future: What Happens When the Algorithm Breaks?
Welcoming Tom Butta as Chief Commercial & Marketing Officer
Post-Quantum Cryptography in 2026: What Infrastructure Leaders Need to Know
Quantum and AI: Twin Threats to Data Security
Nobel Prize Highlights Urgency of Post-Quantum Cryptography
$1 Billion Investment Accelerates CRQC Timeline
RFC 9370: Is It Enough?
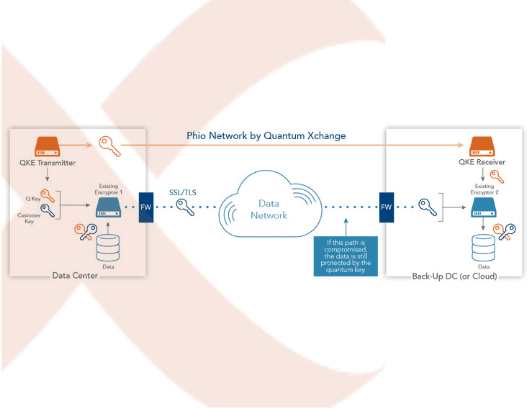
Solving Multi-Protocol Compatibility Issues with Phio TX®
Recapping Cisco Live 2025: Preparing for the Post-Quantum Era
Phio TX-EM: Embracing PQCs Just Got Easier
Post-Quantum Readiness in Risk Assessments
Harvest Now, Decrypt Later: The Quantum Security Threat Hanging Over Today’s Data
2025 Verizon Data Breach Investigations Report: Preparing for the Next Frontier in Cybersecurity
RSAC 2025 Recap
Strategic Product Transition: Our Commitment to Innovation and Partnership
Recommended Quantum Talks at RSA 2025
Healthcare to Benefit Greatly from Quantum Technologies, But Ill Prepared
NIST Releases Backup PQC Algorithm: Reinforces Phio TX Use Case
Microsoft’s Majorana 1: Quantum Computers are Years Not Decades Away
FS-ISAC Issues New Guidance to Help the Payment Card Industry Mitigate Risks of Quantum Computing
The United Nations International Year of Quantum
11th Hour Executive Order to Strengthen U.S. Cyber Practices Buries Quantum Headline: PQC is Now, Not 2035
What Is the Impact of Quantum Computing on Cybersecurity?
Salt Typhoon: A Wake-Up Call for Encryption Management & Control
Google’s Willow Chip Speeds Post-Quantum Migration Timelines: The Time to Act is Now
2025 Outlook: Navigating the Quantum Revolution in 2025 and Beyond
Going Beyond PCI DSS 4.0 to Redefine Cryptographic Compliance in Finance
What Happens If the PQCs Fail? The Continued Case for Crypto Diversification
The NIST PQC Standard: What Enterprises Need to Know
How Quantum Xchange Solves for the PQC Adoption Challenges Outlined by NIST
NIST Updates PQC Guidance: Cryptographic Discovery Using CipherInsights from Quantum Xchange
GSMA Urges Membership to Define Guidelines and Processes for PQC Transition
How to Avoid KyberSlash and Other Vulnerabilities Like It
Quantum Technology’s Impact on the Metaverse
2024 Verizon Data Breach Investigations Report: Third-Party Risk & CipherInsights
Why the Java ECDSA Bug Is Illustrative of a Crypto Monoculture That Must Change: The Case for Crypto Diversification
Single Points of Failure in Cryptography #3: Weak or Low Entropy
Single Points of Failure in Cryptography, Post #6: Bugs in Software
Single Points of Failure in Cryptography #5: The Human Factor
Single Points of Failure in Cryptography #4: Password Strength
Single Points of Failure Debut Post: Public Handshake & Key Derivation
Single Points of Failure in Cryptography #2: Asymmetric Encryption
Our Contribution to The White House PQC Roundtable – Part 1: When (and When Not) to Use Hybrid Encryption
Our Contribution to The White House PQC Roundtable – Part 3: The Cost of Implementing Quantum Cryptography + Enhancing Crypto-Agility
Our Contribution to The White House PQC Roundtable – Part 2: Preparing for Post-Quantum Cryptography
Fortinet’s Next-Gen Firewall Now Supports the ETSI Quantum Key Distribution (EQKD) Protocol
Meeting Federal Mandates: From Quantum Safe to Zero Trust
Attack on Municipal Water Authority Sheds Light on the Importance of Future-Proofing Critical Infrastructure
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #3 – Advantage
Calculating Damages of a Quantum-Enabled Attack on US Financial Systems
Invest in a Resilient Digital Future. Do Your Part, #BeQuantumSafe
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #2 – Anticipation
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #1- Awareness
Break the Crypto Monoculture, Don’t Fall Victim to It
New Year, New Security Priorities – Get Quantum Fit in 2023
Three Predictions for 2023
Phio TX Awarded Patent for Secure Out-of-Band Symmetric Encryption Key Delivery
Cure Ransomware Before the Attack, Not During It
Another NIST PQC Finalist Bites the Dust – The Case for Crypto-Diversification Strengthened
Federal Quantum Mandates Abound – States Take Notice at NYS 24th Annual Cybersecurity Conference
A Brief Guide to Quantum Encryption vs. Post-Quantum Cryptography [INFOGRAPHIC]
Quantum Communications in Real-World Applications
What are Quantum Networks and How Do They Work?
World Quantum Day: Where the Quantum Revolution Stands
The Fifth Domain Takes a Quantum Leap Forward – Why Ongoing Cyber Warfare Could Spark a Quantum Arms Race
Government Closes in on Quantum-Resistant Encryption Standards – Plan for Failure with Quantum-in-Depth Approach
Why BCG’s “Ensuring Online Security in a Quantum Future” is a Must Read for Every Enterprise
A Wake-Up Call for Critical Infrastructure: Lessons from the Florida Water Supply Attack
Love Your Data
Quantum Xchange Receives FIPS 140-2 Validation: Certificate #3754 and #3569
Meet Our New CEO: Eddy Zervigon
NIST Announces PQC Selection Round, Acknowledges Future Consideration of New Approaches
Phio TX Inventor Shares His Favorite Features in Version 2.0
The Race for a COVID-19 Vaccine: Another Opportunity for Chinese IP Theft, Another Reason to Protect Our Critical Data with Quantum Keys
Proposed Presidential FY2021 Budget Validates Importance of Investing in Quantum Technology
There’s No Time to Wait: Security Pros at RSA 2020 Recognize the Urgency of Quantum Readiness But Orgs Fail to Act
What direction will the Internet take in the next 50 years
Achieving Quantum Readiness with Phio TX
Colonial Pipeline Attack in the Quantum Era? An Unthinkable, Yet Very Real, Scenario that Requires Action Today
Countdown to Encryption – Only 120 Days Remain for Meeting the White House Executive Order on Encrypting Data in Motion
The Case for Out-of-Band Key Delivery in Energy’s Critical Infrastructure Protection Plan
Quantum-Safe VPNs are Gaining Momentum and Making Headlines
True Crypto Agility Revisited – Phio TX Bragging Rights
“Act Now” Says DHS/NIST and CSA – Get a Jump on Post-Quantum Planning & Execution
The Role of Quantum Security and its Impact on the Tech Trends Shaping the Next Decade
Public Key Encryption Dead Before 50?
Booz Allen Report: China May Steal Encrypted Government Data Now to Decrypt with Quantum Computers Later
2022’s Top 5 Cybersecurity Trends with a Quantum Twist
NSM-8: Government Mandates Quantum Resistant Cryptography for Protecting Federal Networks
Love Your Data for the Long Haul
Starlink Signal Jamming Signals a Cybersecurity Wake-up Call: Space is at Risk
How Close Are We to a Commercial Quantum Computer?
ETSI QKD – The Little-Known Protocol with Big Security Implications
Load Load
more more
See how Phio TX can protect your critical data-in-motion today and in the post-quantum world.
See See
a a
demo demo






















![A Brief Guide to Quantum Encryption vs. Post-Quantum Cryptography [INFOGRAPHIC]](https://quantumxc.com/wp-content/uploads/Quantum-Post-Quantum-Blog-Images-w_-Watermark.png)