SANS Cyber Security Webinar

Quantum XChange Accelerates Channel Momentum Amid Surging Government Demand for Post-Quantum Cryptography
Quantum XChange’s Platform Supports 3 Gartner Predictions for 2026
Quantum XChange CEO Eddy Zervigon Speaks with MeriTalk on Q-Day, PQC Readiness, and Federal Migration
World Quantum Day 2026: The Threat Is Real, and the Clock Is Ticking
Post-Quantum Cryptography for Banking: A Security Architect’s Guide to a Secure Infrastructure
AI-Powered Vulnerability Discovery Is Here. Is Your Encryption Infrastructure Ready?
The Quantum Security Problem for Big Banks Is Here: Are You Ready?
Quantum XChange Launches Centralized Management Console for Quantum-Safe Key Delivery at Scale
Quantum XChange Launches Centralized Management Console to Deliver Enterprise-Scale Visibility and Control of Quantum-Safe Key Management
Google Moved Up Q-Day. Here’s What to Do About It.
Quantum XChange Wins Gold for Post-Quantum Cryptography
Quantum XChange Wins Gold for Post-Quantum Cryptography in the 2026 Cybersecurity Excellence Awards
When it Comes to Quantum Safety, Sovereignty Demands Architectural Clarity
Quantum XChange Wins 2026 Globee Award for Cybersecurity
Quantum XChange Wins 2026 Globee Award for Cybersecurity
Google Primes Chrome for a Post-Quantum World
2026 Quantum Security: Are You Moving Fast Enough?
Quantum XChange Advances EUCC Milestone and Enterprise Scalability with Latest Release of Phio TX
AI Poised to Outrun Cyber Defenders, Congress Hears
Quantum Cryptography Implementation Timelines Must be Shortened, Industry CEO to Tell Congress
The Quantum-Era Wake-Up Call For Satellite Communications
SANS Institute Validates Quantum XChange’s Phio TX for Quantum-Ready Security and Resilience
SANS Cyber Security Webinar
Phio TX-EM Datasheet
Regional Approaches To Post-Quantum Cryptography
Quantum Xchange Launches Version 4.5 of Its Leading PQC Network Security Solution
Quantum XChange Wins SiliconANGLE TechForward Award
Quantum Xchange Wins SiliconANGLE TechForward Award
Quantum Xchange Urges Government Agencies and Commercial Businesses to Begin PQC Migration Efforts Through a Series of Informative Events
Post-Quantum Cryptography: Beyond The CISO’s Responsibility
Quantum Xchange Grows Headcount By 60% To Meet Global Demand For Its Leading Quantum-Safe Key Management System
8 Steps to Ensure Data Privacy Compliance Across Borders
Beyond Operating Systems: Considerations For A Comprehensive Quantum Security Strategy
Quantum Xchange Releases Virtual Container Key Management Solution for Post-Quantum Cryptography
Ready for a Post-Quantum World? The Time to Start Is Now
Maryland’s Push to Become the World’s Quantum Capital
Keyfactor Bolsters Quantum Readiness with Dual Acquisitions
Making the Most of Cryptography, Now and in the Future
The Cyber Year in Stories: Summer 2024
Quantum Xchange Receives FIPS 203 Validation for its Key Delivery and Management System Phio TX
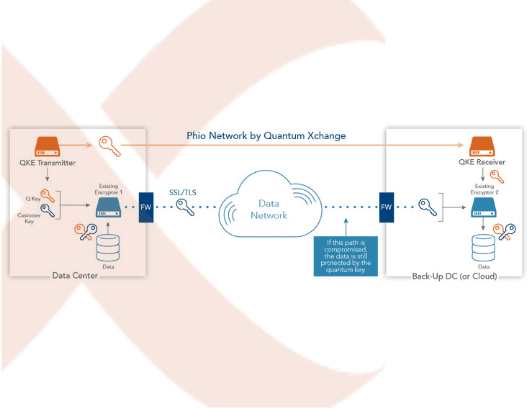
Quantum Xchange Breaks Final Barriers to Make Quantum Key Distribution (QKD) Commercially Viable with the Launch of Phio TX
Quantum Xchange Showcases its Groundbreaking Quantum-Safe Key Management System at MIT Future Compute
Quantum Xchange Receives FIPS 140-2 Validation for its Quantum-Safe Key Management System
Quantum Xchange Adds Post-Quantum Cryptography to Phio TX
Quantum Xchange Named to the Global CyberTech100 List for 2020
Quantum Xchange Releases Version 2.0 of its Quantum-Safe Key Distribution System Featuring New User Interface
Quantum Xchange Named 2020 Cybersecurity Company to Watch by the Cybersecurity Association of Maryland
Quantum Xchange Announces Quantum-Safe Encryption for Hybrid Cloud Environments
Quantum Xchange Completes Initial Series A Funding, Appoints New Business and Technology Leaders to Meet Global Demand for Quantum-Safe Security Solutions
Quantum Xchange Names John N. Stewart, Former Senior Vice President and Chief Security and Trust Officer at Cisco to its Board of Directors
Retired U.S. Army Colonel and Medal of Honor Recipient Jack H. Jacobs Joins Quantum Xchange’s Advisory Board
Quantum Xchange Named to the 2021 Big50 Startup Report
Quantum Xchange Collaborates with Thales to Enable Quantum-Safe Key Delivery Across Any Distance, Over Any Network Media
Quantum Xchange Partners with Spire Solutions to Bring Advanced Quantum-Safe Network Security and Data Protection to the Middle East and Africa
Quantum Xchange Diversifies Cyber Security Global Excellence Award Wins, Bringing Home a Gold and Bronze in 2022
Quantum Xchange Expands Global Presence Inking Partnership with Warpcom to Bring Quantum-Safe Networking to Spain and Portugal
Admiral Mike Rogers Joins Quantum Xchange’s Board of Directors
Quantum Xchange Launches Partner Program to Give Managed Connectivity Providers and Networking-as-a-Service Vendors Competitive Advantage
Quantum Xchange Awarded a 2023 INTERNET TELEPHONY SD-WAN Product of the Year Award
Proprietary Research from Quantum Xchange Shows the Dreadful State of Enterprise Cryptography
Quantum Xchange Joins Migration to Post-Quantum Cryptography Project Consortium
Quantum Xchange Cements Its Standing as a Vital Compliance Arsenal for EU Enterprises
Quantum Xchange and Juniper Networks Partner to Provide Quantum-Safe Network Security Solutions for Highly Regulated Industries
Quantum Xchange Launches First VPN to Combine AI-Native Networking with Quantum Safety
Quantum Xchange Enables Enterprises to Track Progress Toward Post-Quantum Standardization with Dynamic Dashboards
Quantum Xchange Supports All Standard Post-Quantum Algorithms and Migration Recommendations Announced by NIST
Quantum Xchange Recognized as an IDC Innovator for Post-Quantum Cryptography
Quantum Xchange Receives FIPS 140-3 Certification for Phio TX
On Demand: What the NIST PQC Standard Means to Enterprises
Joint Webinar with Thales: Assessing the True Threats and Potential Damage of Quantum Cyberattacks
Telefónica, Fortinet, Quantum Xchange and Warpcom Present Innovative Solution for Quantum Cyberattacks
Eurobites: Telefónica and friends develop quantum-safe cybersecurity tool
Telefónica Unveils Quantum Cyberattack Solution
New Infosec Products of the Week: July 12, 2024
Quantum Xchange Expands Phio TX Platform to Offer Secure Site-to-Site and Remote Access VPN
Quantum Xchange Named a PQC Innovator in Booz Allen Emerging Tech Report
Quantum Xchange Supports All Post-Quantum Standard Finalists Announced by NIST
Quantum Xchange Strengthens Priseda’s National Private Network for Resiliency with Advanced Quantum Security
Quantum Xchange Makes Quantum-Safe Encryption Available and Affordable to Organizations of Any Size with the Launch of Phio TX-D
Quantum Xchange Announces the General Availability of CipherInsights™ for Cryptographic Risk Management
Engage Black and Quantum Xchange Partner to Bring Immediate Quantum-Resistant Capabilities to the BlackDoor Encryptor Suite
10 Defining Moments in Cybersecurity and Satellite in 2022
LTIMindtree Launches and Tests Quantum-Safe VPN Link in London in Collaboration with Quantum Xchange & Fortinet
Cryptography is Dying – Long Live Cryptography
Quantum Xchange Named to Top 100 Next Generation Companies 2023 by the World Future Awards
What You Need to Know to Embrace the Imminent Quantum Shift for Your Cryptography Future
Crypto Asset Discovery and the Post-Quantum Migration
Outdated Cryptographic Protocols Put Vast Amounts of Network Traffic at Risk
Protecting Cross-Border Data Flows with Quantum-Safe Security
Future-Proofing Federal Data & Communications Networks
How to Achieve Cryptographic Clarity and Comply with Leading Data Security and Privacy Standards
Cryptography at the Heart of Cybersecurity: State and Local Governments Lead the Charge
Preparing for the ‘Great Crypto Migration’ by Embracing a Quantum Future
Quantum Xchange Named to Telecom Council’s Innovation Showcase Class of 2023
NaaS Vendors Are On The Front Line To Deliver Quantum-Ready Security
Delivering the Future of Encryption with CryptoDiversification by Phio TX
How to Avoid TLS Harvesting and SSL Scraping Attacks with Phio TX
Quantum Xchange Named Winner in Two Categories for the Coveted Global InfoSec Awards
Quantum Xchange Selects Zayo Group for Dark Fiber to Deploy First Quantum Network in the United States
Renowned Cryptographer Dr. Whitfield Diffie Joins Quantum Xchange’s Advisory Board
Quantum Xchange Gains Industry Momentum; Addresses the Shortcomings of Modern Day Encryption
Quantum Xchange and ID Quantique Make Ultra-Secure Quantum Networks a Reality for Leading U.S. Industries
Delivering the Future of Encryption
Quantum Xchange Named Best of Montgomery County in the 2021 MD Cybersecurity Awards by the Cybersecurity Association of Maryland, Inc.
Quantum Xchange Teams with CommStar to Protect Advanced Earth-to-Moon Communications Infrastructure
Quantum Xchange Named to the Global CyberTech 100 List for the Second Consecutive Year
Quantum Xchange Completes Integration with Cisco to Enable Quantum-Safe Networking Equipment with No Key Delivery Limitations
Quantum Xchange, Toshiba, and Verizon to Share Expert Insights on Deploying Quantum Networks at Inside Quantum Technology New York 2021
Defending Encryption: Quantum XChange at Cisco Live Amsterdam
Confronting a New Reality: Agencies Need to Adopt Cryptographic Agility with New Quantum-Ready Encryption
Quantum XChange Wins 2025 Digital Innovator Award from Intellyx
Securing the Future: What Happens When the Algorithm Breaks?
A Response to NIST’s Post-Quantum Cryptography Adoption Challenges and Planning Requirements
Quantum XChange Recognized as 2024 IDC Innovator for Post-Quantum Cryptography
Welcoming Tom Butta as Chief Commercial & Marketing Officer
Quantum XChange Named to Telecom Council’s Innovation Showcase Class of 2023
eBook: Preparing Your Organization for a Multiyear Post-Quantum Cryptography Transition
Post-Quantum Cryptography in 2026: What Infrastructure Leaders Need to Know
Phio TX: The Only Choice for Quantum Attack Protection
Quantum XChange Wins a 2023 INTERNET TELEPHONY SD-WAN Product of the Year Award
Quantum and AI: Twin Threats to Data Security
How Phio TX Enhances QKD Technology
Nobel Prize Highlights Urgency of Post-Quantum Cryptography
Hardening Guidance for Federal Networks and Communications Infrastructure
Quantum XChange Wins Hot Company Cybersecurity Visionary and Next-Gen Secure Communications in 10th Annual Global InfoSec Awards at #RSAC 2022
$1 Billion Investment Accelerates CRQC Timeline
U.S. Government Mandates on Quantum Preparedness
Quantum XChange Named to Top 100 Next Generation Companies 2023 by the World Future Awards
RFC 9370: Is It Enough?
Quantum XChange Wins World Future Award for Best Enterprise Data Security Solutions 2023
Government Resource Center
Solving Multi-Protocol Compatibility Issues with Phio TX®
Quantum XChange Wins Gold in the 18th Annual 2022 Cyber Security Global Excellence Awards
Recapping Cisco Live 2025: Preparing for the Post-Quantum Era
Quantum Xchange Wins Bronze in the 18th Annual 2022 Cyber Security Global Excellence Awards
Phio TX-EM: Embracing PQCs Just Got Easier
Post-Quantum Readiness in Risk Assessments
Harvest Now, Decrypt Later: The Quantum Security Threat Hanging Over Today’s Data
Phio Product Guide
2025 Verizon Data Breach Investigations Report: Preparing for the Next Frontier in Cybersecurity
RSAC 2025 Recap
Full Visibility, Management, and Control Over Your Enterprise Encryption
Strategic Product Transition: Our Commitment to Innovation and Partnership
Recommended Quantum Talks at RSA 2025
Insurance Compliance & Risk Management
Healthcare to Benefit Greatly from Quantum Technologies, But Ill Prepared
Phio TX-D: Making Quantum-Safe Encryption Available to All
NIST Releases Backup PQC Algorithm: Reinforces Phio TX Use Case
Meet NSM-8 & NSM-10 Quantum-Resistant Encryption Requirements with Phio TX
Microsoft’s Majorana 1: Quantum Computers are Years Not Decades Away
FS-ISAC Issues New Guidance to Help the Payment Card Industry Mitigate Risks of Quantum Computing
The United Nations International Year of Quantum
Fortinet and Quantum Xchange Team to Deliver Quantum-Safe SD-WAN
11th Hour Executive Order to Strengthen U.S. Cyber Practices Buries Quantum Headline: PQC is Now, Not 2035
CryptoDiversification by Phio TX – A Diversified Portfolio of Current and Post-Quantum Encryption Technologies
What Is the Impact of Quantum Computing on Cybersecurity?
Salt Typhoon: A Wake-Up Call for Encryption Management & Control
Google’s Willow Chip Speeds Post-Quantum Migration Timelines: The Time to Act is Now
2025 Outlook: Navigating the Quantum Revolution in 2025 and Beyond
Securing Emerging 5G Global Networks and Mobile Infrastructure
Improving Your Quantum Literacy
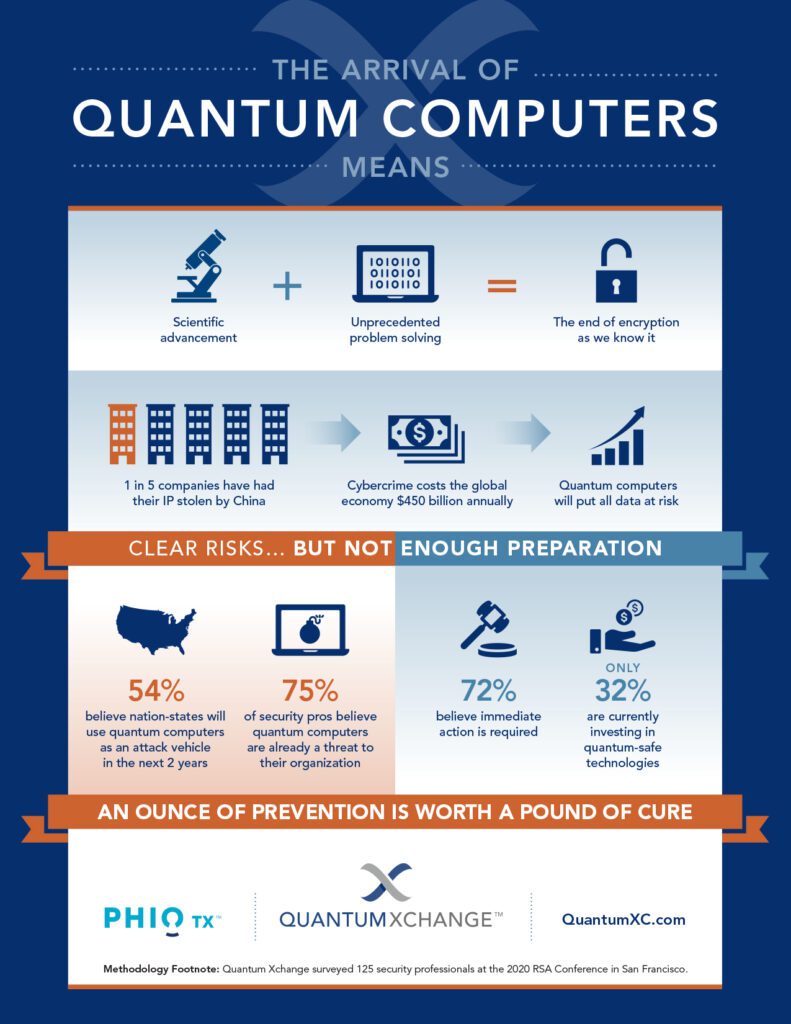
The Arrival of Quantum Computers
Going Beyond PCI DSS 4.0 to Redefine Cryptographic Compliance in Finance
eBook: Single Points of Failure in Cryptography
What Happens If the PQCs Fail? The Continued Case for Crypto Diversification
The NIST PQC Standard: What Enterprises Need to Know
The Quantum Advantage for Managed Connectivity and Networking-as-a-Service Providers
How Quantum Xchange Solves for the PQC Adoption Challenges Outlined by NIST
Ultra-Secure, Quantum-Safe Data Protection for Federal Agencies and Partners
NIST Updates PQC Guidance: Cryptographic Discovery Using CipherInsights from Quantum Xchange
GSMA Urges Membership to Define Guidelines and Processes for PQC Transition
How to Avoid KyberSlash and Other Vulnerabilities Like It
Quantum Technology’s Impact on the Metaverse
Impregnable Cryptographic Solutions for the Ages
2024 Verizon Data Breach Investigations Report: Third-Party Risk & CipherInsights
Why the Java ECDSA Bug Is Illustrative of a Crypto Monoculture That Must Change: The Case for Crypto Diversification
eBook: Making Space Technology Infrastructure and Communications Safe
Single Points of Failure in Cryptography #3: Weak or Low Entropy
Achieving Crypto-Agility and Quantum Readiness with Phio TX
Single Points of Failure in Cryptography, Post #6: Bugs in Software
Cross-Border Data Privacy and Security Concerns in the Dawn of Quantum Computing
Single Points of Failure in Cryptography #5: The Human Factor
Banking on Quantum Computers — The Promise and the Peril
Single Points of Failure in Cryptography #4: Password Strength
Phio TX from Quantum Xchange Makes Thales Network Encryptors Immediately Quantum-Resistant, Bringing to Market the First Quantum-Safe HSE
Single Points of Failure Debut Post: Public Handshake & Key Derivation
Supercharged, Quantum-Safe Security for Critical Infrastructure
Single Points of Failure in Cryptography #2: Asymmetric Encryption
eBook: Incorporate New Data Security and Encryption Methods Into Current Network Infrastructure Projects
Our Contribution to The White House PQC Roundtable – Part 1: When (and When Not) to Use Hybrid Encryption
Our Contribution to The White House PQC Roundtable – Part 3: The Cost of Implementing Quantum Cryptography + Enhancing Crypto-Agility
Our Contribution to The White House PQC Roundtable – Part 2: Preparing for Post-Quantum Cryptography
Fortinet’s Next-Gen Firewall Now Supports the ETSI Quantum Key Distribution (EQKD) Protocol
Meeting Federal Mandates: From Quantum Safe to Zero Trust
Attack on Municipal Water Authority Sheds Light on the Importance of Future-Proofing Critical Infrastructure
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #3 – Advantage
Calculating Damages of a Quantum-Enabled Attack on US Financial Systems
Invest in a Resilient Digital Future. Do Your Part, #BeQuantumSafe
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #2 – Anticipation
Three-Pronged Strategy for a Successful Post-Quantum Migration: Pillar #1- Awareness
Break the Crypto Monoculture, Don’t Fall Victim to It
New Year, New Security Priorities – Get Quantum Fit in 2023
Three Predictions for 2023
Phio TX Awarded Patent for Secure Out-of-Band Symmetric Encryption Key Delivery
Cure Ransomware Before the Attack, Not During It
Another NIST PQC Finalist Bites the Dust – The Case for Crypto-Diversification Strengthened
Federal Quantum Mandates Abound – States Take Notice at NYS 24th Annual Cybersecurity Conference
A Brief Guide to Quantum Encryption vs. Post-Quantum Cryptography [INFOGRAPHIC]
Quantum Communications in Real-World Applications
What are Quantum Networks and How Do They Work?
World Quantum Day: Where the Quantum Revolution Stands
The Fifth Domain Takes a Quantum Leap Forward – Why Ongoing Cyber Warfare Could Spark a Quantum Arms Race
Government Closes in on Quantum-Resistant Encryption Standards – Plan for Failure with Quantum-in-Depth Approach
Why BCG’s “Ensuring Online Security in a Quantum Future” is a Must Read for Every Enterprise
A Wake-Up Call for Critical Infrastructure: Lessons from the Florida Water Supply Attack
Love Your Data
Quantum Xchange Receives FIPS 140-2 Validation: Certificate #3754 and #3569
Meet Our New CEO: Eddy Zervigon
NIST Announces PQC Selection Round, Acknowledges Future Consideration of New Approaches
Phio TX Inventor Shares His Favorite Features in Version 2.0
The Race for a COVID-19 Vaccine: Another Opportunity for Chinese IP Theft, Another Reason to Protect Our Critical Data with Quantum Keys
Proposed Presidential FY2021 Budget Validates Importance of Investing in Quantum Technology
There’s No Time to Wait: Security Pros at RSA 2020 Recognize the Urgency of Quantum Readiness But Orgs Fail to Act
What direction will the Internet take in the next 50 years
Achieving Quantum Readiness with Phio TX
Colonial Pipeline Attack in the Quantum Era? An Unthinkable, Yet Very Real, Scenario that Requires Action Today
Countdown to Encryption – Only 120 Days Remain for Meeting the White House Executive Order on Encrypting Data in Motion
The Case for Out-of-Band Key Delivery in Energy’s Critical Infrastructure Protection Plan
Quantum-Safe VPNs are Gaining Momentum and Making Headlines
True Crypto Agility Revisited – Phio TX Bragging Rights
“Act Now” Says DHS/NIST and CSA – Get a Jump on Post-Quantum Planning & Execution
The Role of Quantum Security and its Impact on the Tech Trends Shaping the Next Decade
Public Key Encryption Dead Before 50?
Booz Allen Report: China May Steal Encrypted Government Data Now to Decrypt with Quantum Computers Later
2022’s Top 5 Cybersecurity Trends with a Quantum Twist
NSM-8: Government Mandates Quantum Resistant Cryptography for Protecting Federal Networks
Love Your Data for the Long Haul
Starlink Signal Jamming Signals a Cybersecurity Wake-up Call: Space is at Risk
How Close Are We to a Commercial Quantum Computer?
ETSI QKD – The Little-Known Protocol with Big Security Implications
Load Load
more more
Have one of our experts show you how Phio TX protects your organization from threats today and the quantum future.
Request Request
a a
demo demo






























































































































![A Brief Guide to Quantum Encryption vs. Post-Quantum Cryptography [INFOGRAPHIC]](https://quantumxc.com/wp-content/uploads/Quantum-Post-Quantum-Blog-Images-w_-Watermark.png)